Hello.
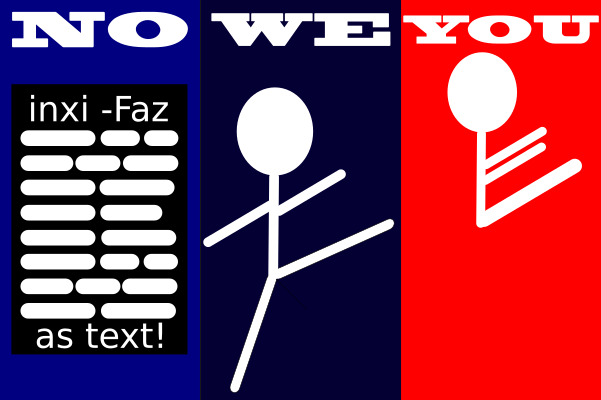
Post your terminal/konsole in- and output as text (no pictures) from:
System: Kernel: 5.13.18-200-tkg-muqss x86_64 bits: 64 compiler: gcc v: 11.1.0
parameters: intel_pstate=passive BOOT_IMAGE=/@/boot/vmlinuz-linux-tkg-muqss-generic_v3
root=UUID=ef15347e-a4da-4628-afc3-2bff20cbb710 rw rootflags=subvol=@ quiet nvidia-drm.modeset=1 splash
rd.udev.log_priority=3 vt.global_cursor_default=0 systemd.unified_cgroup_hierarchy=1
resume=UUID=e7745511-30a0-4b3d-93c1-4bc3daa8b2b8 loglevel=3 sysrq_always_enabled=1 nowatchdog
Desktop: KDE Plasma 5.22.5 tk: Qt 5.15.2 info: latte-dock wm: kwin_x11 vt: 1 dm: SDDM Distro: Garuda Linux
base: Arch Linux
Machine: Type: Desktop Mobo: ASRock model: X470 Taichi serial: <filter> UEFI: American Megatrends v: P3.50 date: 07/18/2019
Battery: Device-1: hidpp_battery_0 model: Logitech Wireless Mouse MX Master 3 serial: <filter>
charge: 100% (should be ignored) rechargeable: yes status: Discharging
CPU: Info: 6-Core model: AMD Ryzen 5 2600X bits: 64 type: MT MCP arch: Zen+ family: 17 (23) model-id: 8 stepping: 2
microcode: 800820D cache: L2: 3 MiB
flags: avx avx2 lm nx pae sse sse2 sse3 sse4_1 sse4_2 sse4a ssse3 svm bogomips: 86395
Speed: 4051 MHz min/max: 2200/3600 MHz boost: enabled Core speeds (MHz): 1: 4051 2: 4071 3: 4048 4: 4057 5: 4061
6: 4069 7: 4062 8: 4067 9: 4066 10: 4041 11: 4065 12: 4057
Vulnerabilities: Type: itlb_multihit status: Not affected
Type: l1tf status: Not affected
Type: mds status: Not affected
Type: meltdown status: Not affected
Type: spec_store_bypass mitigation: Speculative Store Bypass disabled via prctl and seccomp
Type: spectre_v1 mitigation: usercopy/swapgs barriers and __user pointer sanitization
Type: spectre_v2 mitigation: Full AMD retpoline, IBPB: conditional, STIBP: disabled, RSB filling
Type: srbds status: Not affected
Type: tsx_async_abort status: Not affected
Graphics: Device-1: NVIDIA GP104 [GeForce GTX 1080] vendor: Gigabyte driver: nvidia v: 470.74 alternate: nouveau,nvidia_drm
bus-ID: 0e:00.0 chip-ID: 10de:1b80 class-ID: 0300
Display: x11 server: X.Org 1.20.13 compositor: kwin_x11 driver: loaded: nvidia display-ID: :0 screens: 1
Screen-1: 0 s-res: 6400x2160 s-dpi: 102 s-size: 1594x543mm (62.8x21.4") s-diag: 1684mm (66.3")
Monitor-1: HDMI-0 res: 3840x2160 hz: 60 dpi: 52 size: 1872x1053mm (73.7x41.5") diag: 2148mm (84.6")
Monitor-2: DP-0 res: 2560x1080 dpi: 81 size: 798x334mm (31.4x13.1") diag: 865mm (34.1")
OpenGL: renderer: NVIDIA GeForce GTX 1080/PCIe/SSE2 v: 4.6.0 NVIDIA 470.74 direct render: Yes
Audio: Device-1: NVIDIA GP104 High Definition Audio vendor: Gigabyte driver: snd_hda_intel v: kernel bus-ID: 0e:00.1
chip-ID: 10de:10f0 class-ID: 0403
Device-2: Advanced Micro Devices [AMD] Family 17h HD Audio vendor: ASRock driver: snd_hda_intel v: kernel
bus-ID: 10:00.3 chip-ID: 1022:1457 class-ID: 0403
Sound Server-1: ALSA v: k5.13.18-200-tkg-muqss running: yes
Sound Server-2: JACK v: 1.9.19 running: no
Sound Server-3: PulseAudio v: 15.0 running: yes
Sound Server-4: PipeWire v: 0.3.35 running: yes
Network: Device-1: Intel Dual Band Wireless-AC 3168NGW [Stone Peak] driver: iwlwifi v: kernel port: e000 bus-ID: 08:00.0
chip-ID: 8086:24fb class-ID: 0280
IF: wlp8s0 state: down mac: <filter>
Device-2: Intel I211 Gigabit Network vendor: ASRock driver: igb v: kernel port: d000 bus-ID: 0a:00.0
chip-ID: 8086:1539 class-ID: 0200
IF: enp10s0 state: up speed: 1000 Mbps duplex: full mac: <filter>
IF-ID-1: anbox0 state: down mac: <filter>
Bluetooth: Device-1: Intel Wireless-AC 3168 Bluetooth type: USB driver: btusb v: 0.8 bus-ID: 1-9:6 chip-ID: 8087:0aa7
class-ID: e001
Report: bt-adapter ID: hci0 rfk-id: 1 state: up address: <filter>
Drives: Local Storage: total: 2.27 TiB used: 650.86 GiB (27.9%)
SMART Message: Unable to run smartctl. Root privileges required.
ID-1: /dev/nvme0n1 maj-min: 259:4 vendor: Samsung model: SSD 970 EVO 250GB size: 232.89 GiB block-size:
physical: 512 B logical: 512 B speed: 31.6 Gb/s lanes: 4 type: SSD serial: <filter> rev: 2B2QEXE7 temp: 39.9 C
scheme: GPT
ID-2: /dev/nvme1n1 maj-min: 259:0 vendor: Samsung model: SSD 960 EVO 250GB size: 232.89 GiB block-size:
physical: 512 B logical: 512 B speed: 31.6 Gb/s lanes: 4 type: SSD serial: <filter> rev: 3B7QCXE7 temp: 30.9 C
scheme: GPT
ID-3: /dev/sda maj-min: 8:0 vendor: Seagate model: ST2000DX002-2DV164 size: 1.82 TiB block-size: physical: 4096 B
logical: 512 B speed: 6.0 Gb/s type: HDD rpm: 7200 serial: <filter> rev: CC41 scheme: GPT
Partition: ID-1: / raw-size: 215.45 GiB size: 215.45 GiB (100.00%) used: 161.54 GiB (75.0%) fs: btrfs dev: /dev/nvme0n1p2
maj-min: 259:7
ID-2: /boot/efi raw-size: 260 MiB size: 256 MiB (98.46%) used: 563 KiB (0.2%) fs: vfat dev: /dev/nvme0n1p1
maj-min: 259:6
ID-3: /home raw-size: 215.45 GiB size: 215.45 GiB (100.00%) used: 161.54 GiB (75.0%) fs: btrfs dev: /dev/nvme0n1p2
maj-min: 259:7
ID-4: /var/log raw-size: 215.45 GiB size: 215.45 GiB (100.00%) used: 161.54 GiB (75.0%) fs: btrfs
dev: /dev/nvme0n1p2 maj-min: 259:7
ID-5: /var/tmp raw-size: 215.45 GiB size: 215.45 GiB (100.00%) used: 161.54 GiB (75.0%) fs: btrfs
dev: /dev/nvme0n1p2 maj-min: 259:7
Swap: Kernel: swappiness: 133 (default 60) cache-pressure: 50 (default 100)
ID-1: swap-1 type: partition size: 17.18 GiB used: 0 KiB (0.0%) priority: -2 dev: /dev/nvme0n1p3 maj-min: 259:8
ID-2: swap-2 type: zram size: 15.55 GiB used: 1.85 GiB (11.9%) priority: 100 dev: /dev/zram0
Sensors: System Temperatures: cpu: 55.2 C mobo: 37.0 C gpu: nvidia temp: 49 C
Fan Speeds (RPM): fan-1: 0 fan-2: 1456 fan-3: 1316 fan-4: 1507 fan-5: 1232 gpu: nvidia fan: 22%
Power: 12v: N/A 5v: N/A 3.3v: 3.26 vbat: 3.28
Info: Processes: 478 Uptime: 12m wakeups: 2 Memory: 15.55 GiB used: 9.34 GiB (60.1%) Init: systemd v: 249 tool: systemctl
Compilers: gcc: 11.1.0 clang: 12.0.1 Packages: note: see --pkg apt: 0 pacman: 2074 lib: 546 flatpak: 0 Shell: fish
v: 3.3.1 default: Bash v: 5.1.8 running-in: alacritty inxi: 3.3.06
sudo command fails to authenticate after an update I did not set a separate root password when setting up but su does log in. i checked the sudoers file and the line that allows users belonging to wheel to run sudo commands was commented out so I uncommented it with visudo but I still cant log in with sudo. I also tried passwd root and re-entering my password and also passwd zany130 and it still can't login