inxi -Faz:
perl: warning: Setting locale failed.
perl: warning: Please check that your locale settings:
LANGUAGE = "",
LC_ALL = (unset),
LC_ADDRESS = "pt_BR.UTF-8",
LC_NAME = "pt_BR.UTF-8",
LC_MONETARY = "pt_BR.UTF-8",
LC_PAPER = "pt_BR.UTF-8",
LC_IDENTIFICATION = "pt_BR.UTF-8",
LC_TELEPHONE = "pt_BR.UTF-8",
LC_MEASUREMENT = "pt_BR.UTF-8",
LC_TIME = "pt_BR.UTF-8",
LC_NUMERIC = "pt_BR.UTF-8",
LANG = "en_US.UTF-8"
are supported and installed on your system.
perl: warning: Falling back to the standard locale ("C").
System:
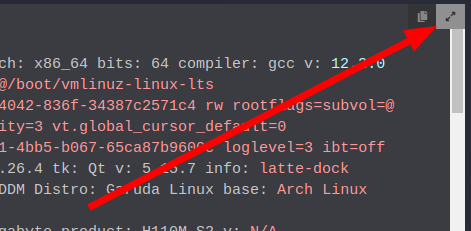
Kernel: 5.15.81-1-lts arch: x86_64 bits: 64 compiler: gcc v: 12.2.0
parameters: BOOT_IMAGE=/@/.snapshots/2131/snapshot/boot/vmlinuz-linux-lts
root=UUID=33da784c-6400-4145-99e3-93bc3c7463b2 quiet
cryptdevice=UUID=5b16040e-5d39-4cd0-80b7-423ffe50eaff:luks-5b16040e-5d39-4cd0-80b7-423ffe50eaff
root=/dev/mapper/luks-5b16040e-5d39-4cd0-80b7-423ffe50eaff splash
rd.udev.log_priority=3 vt.global_cursor_default=0 loglevel=3 ibt=off
rootflags=defaults,noatime,noautodefrag,compress=zstd,subvol=@/.snapshots/2131/snapshot
Desktop: LXQt v: 1.2.0 tk: Qt v: 5.15.7 info: cairo-dock, lxqt-panel
wm: kwin_x11 vt: 1 dm: SDDM Distro: Garuda Linux base: Arch Linux
Machine:
Type: Desktop Mobo: INTEL model: HM65DESK serial: <superuser required>
UEFI: American Megatrends v: 4.6.5 date: 02/23/2019
CPU:
Info: model: Intel Core i7-2620M bits: 64 type: MT MCP arch: Sandy Bridge
gen: core 2 level: v2 built: 2010-12 process: Intel 32nm family: 6
model-id: 0x2A (42) stepping: 7 microcode: 0x2F
Topology: cpus: 1x cores: 2 tpc: 2 threads: 4 smt: enabled cache:
L1: 128 KiB desc: d-2x32 KiB; i-2x32 KiB L2: 512 KiB desc: 2x256 KiB
L3: 4 MiB desc: 1x4 MiB
Speed (MHz): avg: 3193 min/max: 800/3400 scaling: driver: intel_cpufreq
governor: performance cores: 1: 3193 2: 3193 3: 3193 4: 3193 bogomips: 21552
Flags: avx ht lm nx pae sse sse2 sse3 sse4_1 sse4_2 ssse3
Vulnerabilities:
Type: itlb_multihit status: KVM: VMX unsupported
Type: l1tf mitigation: PTE Inversion
Type: mds mitigation: Clear CPU buffers; SMT vulnerable
Type: meltdown mitigation: PTI
Type: mmio_stale_data status: Unknown: No mitigations
Type: retbleed status: Not affected
Type: spec_store_bypass mitigation: Speculative Store Bypass disabled via
prctl and seccomp
Type: spectre_v1 mitigation: usercopy/swapgs barriers and __user pointer
sanitization
Type: spectre_v2 mitigation: Retpolines, IBPB: conditional, IBRS_FW,
STIBP: conditional, RSB filling, PBRSB-eIBRS: Not affected
Type: srbds status: Not affected
Type: tsx_async_abort status: Not affected
Graphics:
Device-1: NVIDIA GM107 [GeForce GTX 750] driver: nvidia v: 525.60.11
alternate: nouveau,nvidia_drm non-free: 520.xx+
status: current (as of 2022-10) arch: Maxwell code: GMxxx
process: TSMC 28nm built: 2014-19 pcie: gen: 1 speed: 2.5 GT/s lanes: 8
link-max: gen: 2 speed: 5 GT/s lanes: 16 bus-ID: 01:00.0
chip-ID: 10de:1381 class-ID: 0300
Display: x11 server: X.Org v: 21.1.4 with: Xwayland v: 22.1.5
compositor: kwin_x11 driver: N/A display-ID: :0 screens: 1
Screen-1: 0 s-res: 1360x768 s-dpi: 90 s-size: 384x300mm (15.12x11.81")
s-diag: 487mm (19.18")
Monitor-1: HDMI-0 res: 1360x768 hz: 60 dpi: 49
size: 708x398mm (27.87x15.67") diag: 812mm (31.98") modes: N/A
API: OpenGL v: 4.6.0 NVIDIA 525.60.11 renderer: NVIDIA GeForce GTX
750/PCIe/SSE2 direct render: Yes
Audio:
Device-1: Intel 6 Series/C200 Series Family High Definition Audio
driver: snd_hda_intel v: kernel bus-ID: 00:1b.0 chip-ID: 8086:1c20
class-ID: 0403
Device-2: NVIDIA GM107 High Definition Audio [GeForce 940MX]
driver: snd_hda_intel v: kernel pcie: gen: 2 speed: 5 GT/s lanes: 8
link-max: lanes: 16 bus-ID: 01:00.1 chip-ID: 10de:0fbc class-ID: 0403
Sound API: ALSA v: k5.15.81-1-lts running: yes
Sound Server-1: PulseAudio v: 16.1 running: no
Sound Server-2: PipeWire v: 0.3.61 running: yes
Network:
Device-1: Realtek RTL8111/8168/8411 PCI Express Gigabit Ethernet
driver: r8169 v: kernel pcie: gen: 1 speed: 2.5 GT/s lanes: 1 port: d000
bus-ID: 03:00.0 chip-ID: 10ec:8168 class-ID: 0200
IF: enp3s0 state: down mac: <filter>
Device-2: Ralink MT7601U Wireless Adapter type: USB driver: mt7601u
bus-ID: 2-1.5:3 chip-ID: 148f:7601 class-ID: 0000 serial: <filter>
IF: wlp0s29u1u5 state: up mac: <filter>
Drives:
Local Storage: total: 2.78 TiB used: 227.42 GiB (8.0%)
SMART Message: Unable to run smartctl. Root privileges required.
ID-1: /dev/sda maj-min: 8:0 model: SATA SSD size: 55.9 GiB block-size:
physical: 512 B logical: 512 B speed: 3.0 Gb/s type: SSD serial: <filter>
rev: Sb10 scheme: GPT
ID-2: /dev/sdb maj-min: 8:16 vendor: Seagate model: ST3000NM0053
size: 2.73 TiB block-size: physical: 512 B logical: 512 B speed: 3.0 Gb/s
type: HDD rpm: 7200 serial: <filter> rev: G00A scheme: GPT
Partition:
ID-1: / raw-size: 558.79 GiB size: 558.79 GiB (100.00%)
used: 227.19 GiB (40.7%) fs: btrfs dev: /dev/dm-0 maj-min: 254:0
mapped: luks-5b16040e-5d39-4cd0-80b7-423ffe50eaff
ID-2: /boot/efi raw-size: 5.59 GiB size: 5.58 GiB (99.80%)
used: 241.4 MiB (4.2%) fs: vfat dev: /dev/sda2 maj-min: 8:2
ID-3: /home raw-size: 558.79 GiB size: 558.79 GiB (100.00%)
used: 227.19 GiB (40.7%) fs: btrfs dev: /dev/dm-0 maj-min: 254:0
mapped: luks-5b16040e-5d39-4cd0-80b7-423ffe50eaff
ID-4: /var/log raw-size: 558.79 GiB size: 558.79 GiB (100.00%)
used: 227.19 GiB (40.7%) fs: btrfs dev: /dev/dm-0 maj-min: 254:0
mapped: luks-5b16040e-5d39-4cd0-80b7-423ffe50eaff
ID-5: /var/tmp raw-size: 558.79 GiB size: 558.79 GiB (100.00%)
used: 227.19 GiB (40.7%) fs: btrfs dev: /dev/dm-0 maj-min: 254:0
mapped: luks-5b16040e-5d39-4cd0-80b7-423ffe50eaff
Swap:
Kernel: swappiness: 133 (default 60) cache-pressure: 100 (default)
ID-1: swap-1 type: zram size: 3.79 GiB used: 94.8 MiB (2.4%) priority: 100
dev: /dev/zram0
Sensors:
System Temperatures: cpu: 44.0 C mobo: N/A gpu: nvidia temp: 38 C
Fan Speeds (RPM): N/A gpu: nvidia fan: 33%
Info:
Processes: 223 Uptime: 2m wakeups: 0 Memory: 3.79 GiB used: 1.74 GiB (45.8%)
Init: systemd v: 252 default: graphical tool: systemctl Compilers:
gcc: 12.2.0 alt: 11 clang: 14.0.6 Packages: 1800 pm: pacman pkgs: 1762
libs: 537 tools: octopi,pamac,paru pm: flatpak pkgs: 38 Shell: Bash
v: 5.1.16 running-in: qterminal inxi: 3.3.23
Hey, me again. This grub update can’t give me a rest. So, last week I’ve had this same problem, but as I immediately went for a snapshot, and then the snapshot recover went wrong, I guess I didn’t really solved my problem? Here’s the previous post:
But after recovering my system I forgot I restored a snapshot and didn’t update. Today my system told me it was out of date and I tried updating… but well, grub is being weird again.
I mean, I can get up to grub and select the Garuda entry, and I go past kernel and initram, but instead of getting the usual plymouth thing, I get only the header as usual, and then a fail, like so:
setfont: KDFONTOP: Function not implemented.
ERROR: device '/dev/mapper/luks-5c18030e-5d39-4cd0-60k7-423ffe50eaff' not found. Skipping fsck.
mount: /new_root: no filesystem type specified.
You are now being dropped into an emergency shell.
sh: can't access tty: job control turned off
[rootfs ]#
That’s about it. I currently can boot into any snapshot, but haven’t tried recovering any of them because, well, I did that last week and it didn’t solve much apparently.
I truly need some help recovering the system and absolutely need help updating my grub properly without breaking everything before I go actually critically out of date.